
Lionakis Accelerates Projects and Prevents Disruption with Egnyte
Lionakis Accelerates projects and Prevents Disruption With Egnyte
Read →
Lionakis Accelerates projects and Prevents Disruption With Egnyte
Read →
Harness the Power of Data to Transform Traditional Practices Most AEC professionals rely on years of experience and instinct. The advent of a centralized, cloud platform has led to a paradigm shift, with data now driving decisions. Egnyte’s Beyond Blueprints Ebook outlines how to embrace the change and harness the power of data for:• Secure […]
Read →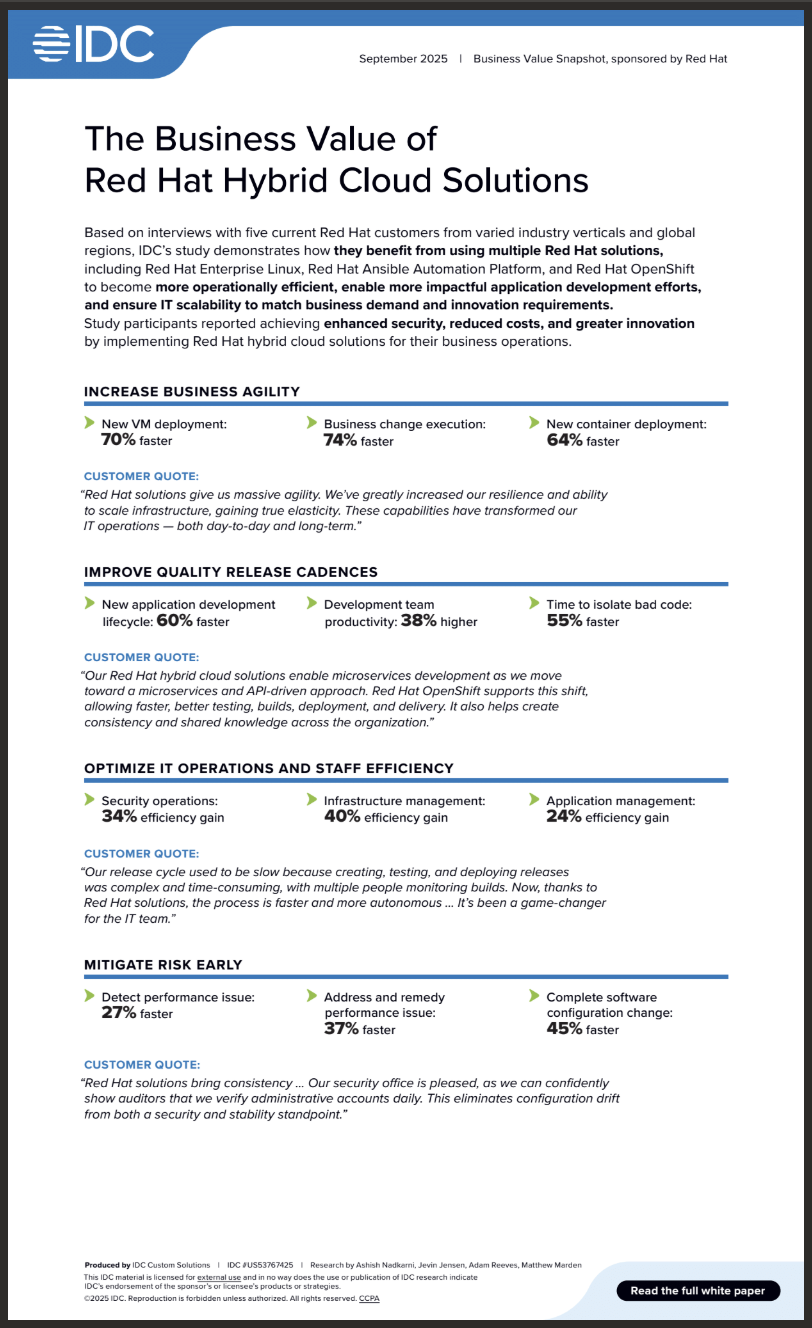
Learn how 5 Red Hat customers from diverse industries achieved operational efficiency, improved application development efforts, and ensured IT scalability by using Red Hat Enterprise Linux, Red Hat Ansible Automation Platform, and Red Hat OpenShift.
Read →
Learn how organizations realize business and IT value and operational efficiency by using Red Hat Enterprise Linux, Red Hat Ansible Automation Platform, and Red Hat OpenShift in their hybrid cloud environments.
Read →
Find out how 7 innovative customers turned their ambitions for adopting AI and automation and launching new services into reality with Red Hat.
Read →
AI is the greatest forcing function in recent decades, driving IT organizations to rethink everything. IT leaders face the challenge of balancing innovation with stability and practicality. In this unsettled time of massive technological change, how can they make smart, strategic decisions that ensure their organization’s long-term success? Join futurist and coauthor of The Driver […]
Read →
Micro-credentials are driving student success, meeting industry demand, and transforming higher education institutions. Employers in the United States (US) are gravitating toward hiring candidates with micro-credentials, citing cost savings, enhanced productivity, and validated skills as top benefits. Many emphasize the need for robust accreditation frameworks to ensure consistent quality. Learn more about how you can […]
Read →
The 2025 Learner Outcomes Report features insights from over 52,000 learners across 179 countries. Created in collaboration with The Harris Poll, the report demonstrates that Coursera and its partners are helping learners advance their careers around the world. The numbers speak for themselves—investing in scalable online learning drives measurable impact, with 91% of learners achieved […]
Read →
Identity is frequently the weakest link in modern cybersecurity programs. As human, non-human, and AI-based identities multiply across hybrid and multi-cloud environments, organizations face growing pressure to maintain visibility, enforce least-privilege access and respond to threats in real time. Identity Security Posture Management (ISPM) has emerged as a go-to solution for these challenges. ISPM blends […]
Read →
Simplify policy creation. Strengthen privileged account security. A ready-to-use policy template for faster compliance and better protection Building a Privileged Access Management (PAM) policy from the ground up takes time and resources — and leaves room for gaps. That’s why Delinea created the Privileged Account Management Policy Template: a customizable framework with over 40 pre-written security […]
Read →
VPNs aren’t protecting your remote workforce Why Remote Privileged Access Management (RPAM) is the smarter path forward Traditional VPNs were designed for a different era — and they’re failing modern organizations. Studies show that more than half of people using a VPN have experienced a cyberattack. Here’s why VPNs fall short: they open wide tunnels […]
Read →
Stop credential attacks before they stop you Why PAM is your best defense against a growing threat Credential-based attacks are a near certainty in today’s threat environment. Recent data shows: 80% of companies experience a credential-based attack each year — and 93% suffer measurable losses. Privileged credentials are often the entry point. If they’re not […]
Read →